How We Solve Our Password Madness
The password problem
Every company with more than a single employee most likely has encountered the following problem: An employee creates a new account on some website to be used by everyone in the company. Afterwards the credentials are sent via email to all colleagues. Nobody will read that email, they don't need it right away, and nobody will find the email in case the account credentials are needed later.
Most importantly - the email is not encrypted and its content is far from anything "secure".
Goals
So we were looking for a solution that offers at least the following points:
- Store company related passwords in a secure manner
- Simplify password sharing in a secure manner
- Reduce overhead for password communication
- Safe time for password administration, simplify login processes
- Have an overview which passwords are shared with whom
- Allow password reset procedures if users are leaving / joining the company
We considered KeePass and 1Password and putting the password vault somewhere into the cloud. In the end, we decided on LastPass Enterprise which some of us already had positive experiences with.
LastPass is a browser based password vault, it has plugins for all major browsers and also synchronizes with mobile devices. Two factor authentication with various methods is included, even with free (non-paid) accounts. LastPass offers shared folders, users with different access rights to shared folders and a wide range of configuration policies and administration features.
Multifactor authentication
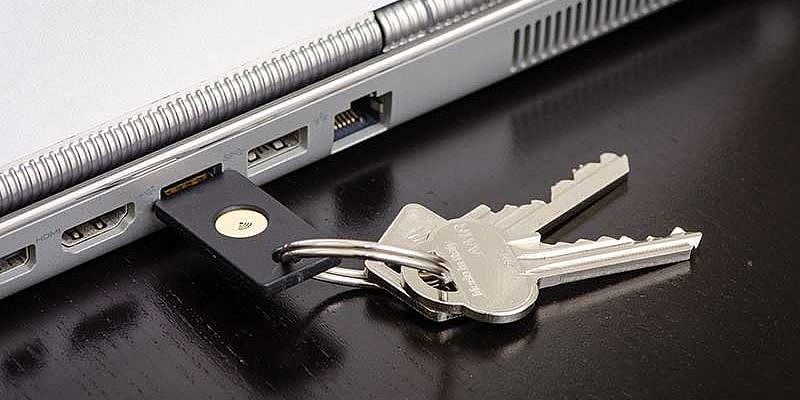
A password is only one factor of authentication and it could become public for various reasons. To secure your account you should rely on a second factor. There are several ways of establishing a second factor of authentication for your password vault, like an RSA token or the LastPass Authenticator App. We use a third option, the YubiKey NEO for every employee, because that is the most convenient second factor device we are aware of. And the YubiKey NEO is able to emit NFC so we could reuse it on all our phones to unlock the vaults from there, as well.
Password storing and sharing
Shared passwords are stored in folders. Every user has access to all shared folders they need to get work done. Some example of such folders:
- Shared - Everyone
Abstract: Shared passwords nearly everyone needs and that are not too risky to give to everyone
Examples: WiFi passwords, office door access code - Shared - Purchasing
Abstract: Accounts needed to purchase goods
Examples: Amazon, Microsoft license management, Adobe license management, LastPass - Shared - Social Media
Abstract: Marketing related accounts like blog administration, camp orga, social media accounts
Examples: Facebook, Twitter, typo3.com blog administration
Other folders could be Internal Servers and Accounts, Customer XYZ, HR ...
In addition, every user has their own personal folder to store personal work-related(!) passwords like personal Jira or TYPO3 instance logins.
Policies
The LastPass Enterprise account allows setting policies to allow or restrict certain functionality. For instance, we force each employee to use a multi factor authorization to login to LastPass.
We added a couple of additional policies in addition to the default ones. As an insight to this feature rich system within LastPass, these are our main policies:
- Account Recovery Email
Every time a user requests the reset of their password, our internal LastPass admins receive an email. - Minimum Number of Different Character Sets in Password
We want to have at least upper case, lower case and numbers in every password. Special characters are optional, but the "create new password" function of the browser plugin will throw them in by default. - Only allow a single YubiKey per account
This is important, otherwise employees could buy a second device and would have access to their business account even if a YubiKey is confiscated for some reason. - Password Length Restriction
At least 8 characters. - Prevent Multifactor Disable via Email
If someone messes with second factor, admins should know. - Prohibit Export
By default every user is able to export all keys in the vault as CSV file. It is obvious why you wouldn't want that in your company. We excluded our admins from that rule, because they should be able to create backups of the vault. - Prohibit Shared Folders Outside Enterprise
That's a topic of constant discussion. With that policy enabled, employees aren't able to share folders in a secure manner with LastPass using outside parties like the customer. So we are forced to communicate passwords with external sources via email. Not perfect, but we will see how that works out. - Prohibit Sharing
Prohibit Sharing Except for Shared Folders
The first policy is to prevent users from creating other shared folders than the ones created by the administrators. The second one is to prevent them from sharing credentials in their own vault. So every shared password is in one of the predefined folders. Keeping things cleaner. - Require use of any multifactor option
No exceptions.
Private personal passwords
Next to personal logins and company work related sites, users typically have tons of private passwords to deal with. We know that our employees will check their social media and buy some Christmas gifts during working hours. That's for sure and something we can live with. And we want to encourage them to always use secure passwords. But we don't want our employees to store their private passwords in the business vault. That would result in discussions when the user leaves the company or is on vacation where they should not use their business account.
LastPass offers a pretty neat feature to link a private account with the enterprise account. When you log in with your business account, you will see all your passwords, private and business alike. When you log in to your private account, you will only see the private passwords. We suggest to our employees to create a private LastPass Account (that's free in the basic plan and costs a buck per month in the premium plan) to store all their private passwords. When the user leaves the company, the private and the company account can be unlinked again and the employee walks away with their private stuff, but leaves personal company passwords.
ATTENTION: Make it clear to your users, that this is a convenience feature, that lowers the private security a bit. There is a theoretical possibility for company admins to hijack a users account and get access to their private passwords. But that would always be noticed, it creates a lot of notification mails and in the end the user can't log in with his own password, because it was changed during the process. So the villain would be caught immediately (and will face the consequences like being fired, get sued and so on) and the user knows what passwords where compromised and need to be changed.
Comments
Hey Guys,
Thank you very much for sharing your solution for password madness ;)
Till date, we're using 1Password but not that much satisfcation. We will surely checkout 'lastpass' tool for the same.
Using LastPass too already long time I see no need to allow passwords short than 16-20 characters. There exist browser-plugins that fill the usernames and passwords on corresponding websites automatically and there is no need to type anything as long as the accounts can be opened inside the browser-window.
Clicking on managing or edit the password can be copied and even entered in other Programs / Apps i.e. any messenger or DBMS.
The option YubiKey and some other details are new for me, so it's good having a short but extensive description with this article.